A silent predator is currently stalking the Apple ecosystem, bypassing years of traditional security assumptions with a single click.
Millions of iPhones at Risk 🚨 New ‘DarkSword’ Spyware Discovered is not just a headline; it is a direct warning to anyone running outdated firmware in 2026.
Our analysis suggests that this “hit-and-run” exploit is fundamentally different from the slow-burn surveillance we have seen in previous years.
Key Takeaways: The DarkSword Threat
- Zero-Click Potential: The spyware can infect a device simply by visiting a compromised website through Safari.
- Massive Scale: Cybersecurity firms estimate that between 220 million and 270 million devices remain vulnerable due to unpatched software.
- Financial & State Motives: Unlike previous spyware, DarkSword actively targets cryptocurrency wallets alongside personal messages and location data.
What exactly is the DarkSword spyware?
If you have been following the Apple ecosystem, this discovery might feel like a recurring nightmare.
DarkSword is a sophisticated, JavaScript-based exploit kit that leverages a chain of six different vulnerabilities.
Industry insiders are noting that it targets iPhones running iOS 18.4 through iOS 18.7, versions many users haven’t yet moved away from.
Once a user lands on an infected “watering hole” website, the malware siphons off everything from Wi-Fi passwords to iPhone camera and microphone settings within minutes.
The most chilling part?
It deletes its own files and exits the system after exfiltrating data, leaving almost no trace for the average user to find.
Is your device on the danger list?
We found that the risk is highest for those who haven’t updated to the latest iOS 26.3 release.
While Apple has been proactive with security, the sheer volume of “legacy” users on iOS 18 creates a massive playground for threat actors.
The following table breaks down the versions currently under fire:
| iOS Version | Risk Level | Primary Vulnerability |
| iOS 18.4 – 18.6.2 | Critical | JavaScriptCore & WebKit Exploits |
| iOS 18.7 | High | Kernel Memory Corruption |
| iOS 26.3 & Later | Low | Patched (Safe) |
Our team observed that even if you have the latest hardware, software negligence is the primary gateway for this attack.
If you are still using an older model, you might want to check the iPhone 11 update cycle to see if your device can even support the necessary patches.
How are hackers using this against you?
We have seen reports of this toolkit appearing on legitimate news sites and government portals in Ukraine and Malaysia.
These are not your typical “suspicious” links; these are trusted domains that have been secretly compromised to host malicious iFrames.
The malware is designed for speed, often finishing its work before you’ve even finished reading the page you visited.
Beyond just reading your texts, it seeks out iCloud Drive files and contacts to map out your digital life.
It’s a professional-grade platform that experts believe was developed with the help of Large Language Models (LLMs) to speed up its deployment.
Steps you must take to stay safe
Don’t wait for a notification that may never come.
We recommend a proactive stance to ensure your digital identity remains locked down.
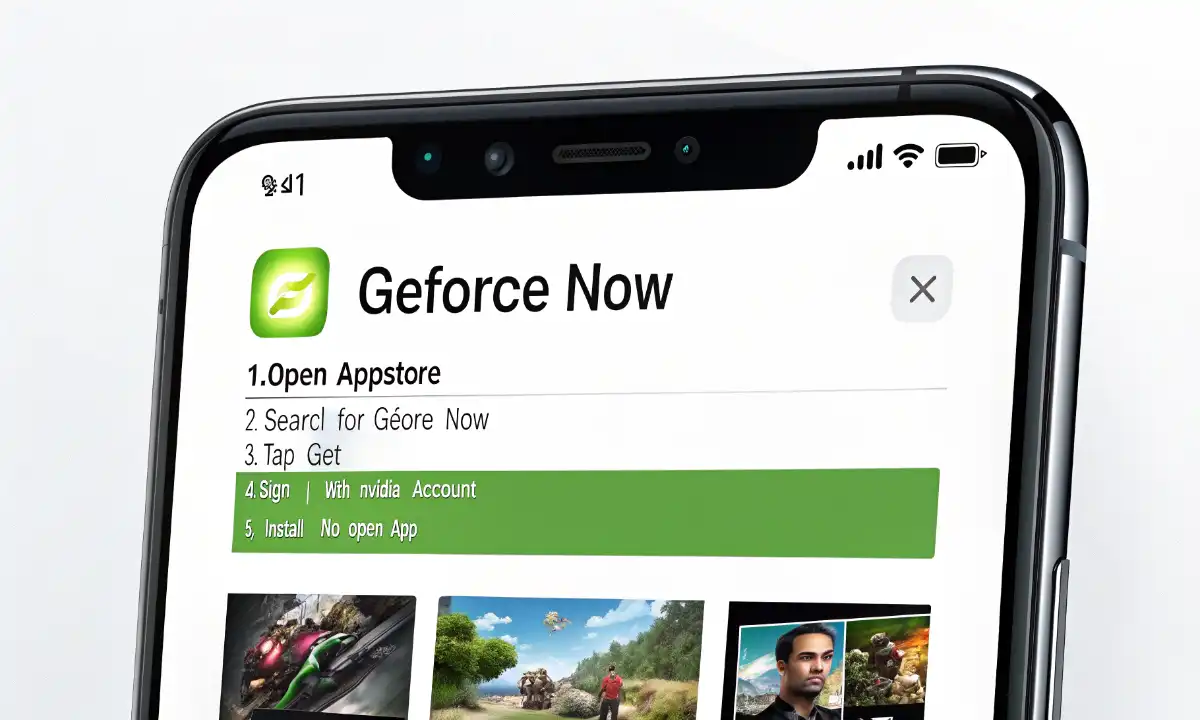
- Update Immediately: Go to Settings > General > Software Update and install the latest available version (ideally iOS 26.3.1 or later).
- Enable Lockdown Mode: If you are a high-risk individual, this feature provides extreme protection by stripping back web functionalities.
- Clear Safari Data: Periodically clearing your cache can help remove lingering tracking elements.
- Review App Permissions: Check your iPhone backup and storage settings to ensure no unauthorized data is being staged for exfiltration.
The “Natural” Evolution of iPhone Hacking
The discovery of DarkSword, alongside the recently disclosed Coruna kit, suggests that the market for “mass” iOS exploits is flourishing.
It is no longer just about state-level intelligence; it is about high-volume data theft.
As we look at the latest Apple news and leaks, it’s clear that security is becoming the primary battlefield for the brand’s survival in 2026.
According to researchers at Google Threat Intelligence and Lookout, the “DarkSword” developers aren’t even trying to hide their tracks anymore, indicating they have plenty of other zero-day exploits waiting in the wings.
Read More: